Important! When using the web interface as shown above, you need to leave the blade open while it assigns permissions. If you navigate away and close it before it completes, the process will get interrupted.
Defining ADLS Data Permissions via PowerShell Script
The technique shown above in the portal is convenient for quick changes, for learning, or for "one-off" scenarios. However, in an enterprise solution, or a production environment, it's a better practice to handle permissions via a script so you can do things such as:
Promote changes through different environments
Pass off scripts to an administrator to run in production
Include permission settings in source control
The two scripts below (option 1 is for groups; option 2 is for users) are split into 4 sub-steps. You might not need all these steps (for instance, if you want to specify permissions at the root level rather than at a subfolder level which is done in the example below).
Important! Definitely make sure to assign the default entries as well as the access entries or you’ll run into problems (the default entries are part of step 4 below). If you were to accidentally set an access entry for a folder without any sort of default entry, new files which are added to the folder won’t have permissions (thus making the files ‘invisible’ to users).
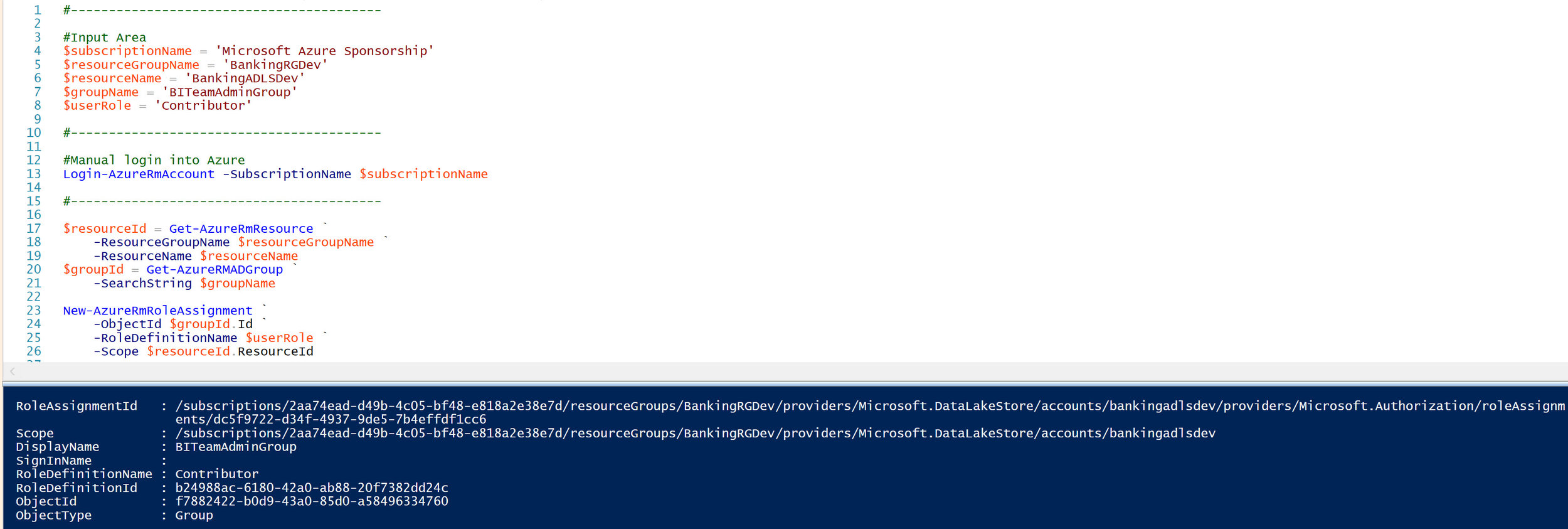
Option 1 - Permissions at the Group Level (recommended)
#This script sets ADLS data-level permissions for one or more AAD groups.
#It is a basic ad hoc script (without error handling, etc).
#Script last tested with PowerShell version 5.1 on Jan 6, 2019.
#-----------------------------------------
#Input Area
#-----------------------------------------
$subscriptionName = 'Microsoft Azure Sponsorship'
$dataLakeStoreName = 'bankingadlsdev.azuredatalakestore.net'
$groupNameArray = @('DataReaderGroup','DataWriterGroup')
$adlsPermissionType = 'Group'
$adlsTraversePermission = 'ReadExecute'
$adlsPathPermission = 'All' #All = Read,Write,Execute
$adlsRoot = '/'
$adlsPath1 = '/ATMMachineData'
$adlsPath2 = '/ATMMachineData/StandardizedData'
#-----------------------------------------
#Manual login into Azure
#-----------------------------------------
#Login-AzureRmAccount -SubscriptionName $subscriptionName
#-----------------------------------------
#Step 1: Set root permissions to traverse
#-----------------------------------------
Write-Host '[*] Begin setting the root permissions to traverse (execute only).'
ForEach ($groupName in $groupNameArray)
{
$groupId = Get-AzureRmADGroup -DisplayName $groupName
Set-AzureRmDataLakeStoreItemAclEntry `
-AccountName $dataLakeStoreName `
-Path $adlsRoot `
-AceType $adlsPermissionType `
-Permissions $adlsTraversePermission `
-Id $groupId.Id
Write-Host "[*] Complete setting root permissions for $groupName."
}
#-----------------------------------------
#Step 2: Set parent folder permissions to traverse
#-----------------------------------------
Write-Host '[*] Begin setting parent folder permission to traverse (execute only).'
ForEach ($groupName in $groupNameArray)
{
$groupId = Get-AzureRmADGroup -DisplayName $groupName
Set-AzureRmDataLakeStoreItemAclEntry `
-AccountName $dataLakeStoreName `
-Path $adlsPath1 `
-AceType $adlsPermissionType `
-Permissions $adlsTraversePermission `
-Id $groupId.Id
Write-Host "[*] Complete setting parent folder permissions for $groupName."
}
#-----------------------------------------
#Step 3: Set ACLs recursively
#-----------------------------------------
Write-Host '[*] Begin setting the ACL (All permissions set recursively on all child items).'
ForEach ($groupName in $groupNameArray)
{
$groupId = Get-AzureRmADGroup -DisplayName $groupName
Set-AzureRmDataLakeStoreItemAclEntry `
-AccountName $dataLakeStoreName `
-Path $adlsPath2 `
-AceType $adlsPermissionType `
-Permissions $adlsPathPermission `
-Id $groupId.Id `
-Recurse `
-Concurrency 128
Write-Host "[*] Complete setting ACLs for $groupName."
}
#-----------------------------------------
#Step 4: Set default entries recursively
#-----------------------------------------
Write-Host '[*] Begin setting the default entry so any new items under this path will obtain the access.'
ForEach ($groupName in $groupNameArray)
{
$groupId = Get-AzureRmADGroup -DisplayName $groupName
Set-AzureRmDataLakeStoreItemAclEntry `
-AccountName $dataLakeStoreName `
-Path $adlsPath2 `
-AceType $adlsPermissionType `
-Permissions $adlsPathPermission `
-Id $groupId.Id -Default `
-Recurse `
-Concurrency 128
Write-Host "[*] Complete setting default entries for $groupName."
}
Option 2 - Permissions at the User Level
#This script sets ADLS data-level permissions for one or more AAD users.
#It is a basic ad hoc script (without error handling, etc).
#Script last tested with PowerShell version 5.1 on Jan 6, 2019.
#-----------------------------------------
#Input Area
#-----------------------------------------
$subscriptionName = 'Microsoft Azure Sponsorship'
$dataLakeStoreName = 'bankingadlsdev.azuredatalakestore.net'
$userNameArray = @('WayneWriter@sqlchick.com','RayReader@sqlchick.com')
$adlsPermissionType = 'User'
$adlsTraversePermission = 'ReadExecute'
$adlsPathPermission = 'All' #All = Read,Write,Execute
$adlsRoot = '/'
$adlsPath1 = '/ATMMachineData'
$adlsPath2 = '/ATMMachineData/StandardizedData'
#-----------------------------------------
#Manual login into Azure
#-----------------------------------------
Login-AzureRmAccount -SubscriptionName $subscriptionName
#-----------------------------------------
#Set the data / POSIX/ ACL permissions
#-----------------------------------------
Write-Host '[*] Begin setting the root permissions to traverse (execute only).'
ForEach ($userName in $userNameArray)
{
$userId = Get-AzureRmADUser -UPN $userName
Set-AzureRmDataLakeStoreItemAclEntry `
-AccountName $dataLakeStoreName `
-Path $adlsRoot `
-AceType $adlsPermissionType `
-Permissions $adlsTraversePermission `
-Id $userId.Id
Write-Host "[*] Complete setting root permissions for $userName."
}
Write-Host '[*] Begin setting the parent folder permission to traverse (execute only).'
ForEach ($userName in $userNameArray)
{
$userId = Get-AzureRmADUser -UPN $userName
Set-AzureRmDataLakeStoreItemAclEntry `
-AccountName $dataLakeStoreName `
-Path $adlsPath1 `
-AceType $adlsPermissionType `
-Permissions $adlsTraversePermission `
-Id $userId.Id
Write-Host "[*] Complete setting root permissions for $userName."
}
Write-Host '[*] Begin setting the ACL (All permissions set recursively on all child items).'
ForEach ($userName in $userNameArray)
{
$userId = Get-AzureRmADUser -UPN $userName
Set-AzureRmDataLakeStoreItemAclEntry `
-AccountName $dataLakeStoreName `
-Path $adlsPath2 `
-AceType $adlsPermissionType `
-Permissions $adlsPathPermission `
-Id $userId.Id `
-Recurse `
-Concurrency 128
Write-Host "[*] Complete setting root permissions for $userName."
}
Write-Host '[*] Set the default entry so any new items under this path will obtain the access.'
ForEach ($userName in $userNameArray)
{
$userId = Get-AzureRmADUser -UPN $userName
Set-AzureRmDataLakeStoreItemAclEntry `
-AccountName $dataLakeStoreName `
-Path $adlsPath2 `
-AceType $adlsPermissionType `
-Permissions $adlsPathPermission `
-Id $userId.Id -Default `
-Recurse `
-Concurrency 128
Write-Host "[*] Complete setting root permissions for $userName."
}
Finding More Information
PowerShell Cmdlets for Azure Data Lake Store
Breaking Changes to Data Lake Store Cmdlets
Access Control in Azure Data Lake Store <--Definitely take time to read this
Secure Data in Azure Data Lake Store